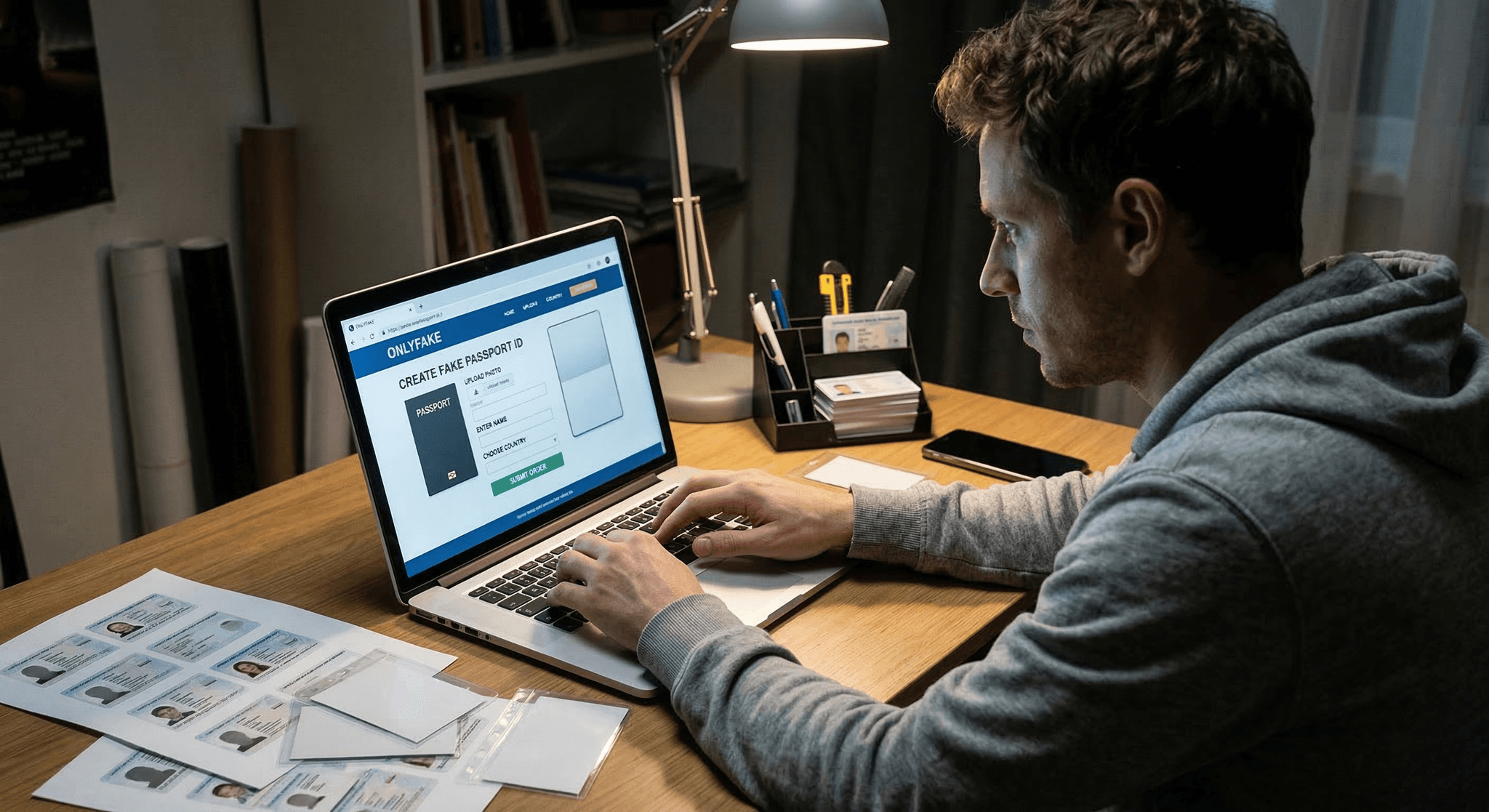
The Rise of Synthetic Document Fraud: What the “OnlyFake” Case Reveals
Fraud powered by digital manipulation is no longer theoretical. It is already happening at scale. According to the U.S. Department of Justice, the service called "OnlyFake" generated more than 10,000 fake digital IDs used by customers worldwide.
Fraud powered by digital manipulation is no longer theoretical. It is already happening at scale.
Recently, U.S. federal prosecutors announced charges against the creator of a service called “OnlyFake,” a platform that sold thousands of fraudulent identification documents online. According to the U.S. Department of Justice, the service generated more than 10,000 fake digital IDs used by customers worldwide.
These were not crude fakes.
Customers could customize the exact format of the fake ID, including whether it looked like:
- A scanned ID document
- A photograph of an ID placed on a table
- A digital copy of passports or driver's licenses
The service allowed users to generate fake versions of U.S. driver’s licenses, passports, Social Security cards, and IDs from dozens of countries.
Fraudsters even had the option to purchase bulk packages of up to 1,000 fake IDs, paying in cryptocurrency.
This is a critical signal for banks, lenders, and insurers.
Fraud is no longer limited to stolen identities or simple document forgery. Today, criminals can generate convincing digital documents on demand and at scale.
The Hidden Risk: Fraud Already in Your Data
Most organizations focus on preventing fraud in new applications.
But the bigger question may be this:
How many manipulated documents already exist inside your historical customer database?
Across lending and insurance portfolios, manipulated documents often remain undetected for years. These can include:
- Pay stubs
- Bank statements
- Driver’s licenses
- Utility bills
- Receipts
- Claim photos
Even a small percentage of manipulated files can translate into millions in risk exposure across large portfolios.
Why Traditional Controls Miss This
Traditional fraud detection typically focuses on:
- OCR validation
- Rule-based checks
- Manual review
But sophisticated document manipulation can bypass these controls because the file looks legitimate to the human eye.
Advanced forensic analysis is needed to detect signals such as:
- Layer inconsistencies
- Metadata manipulation
- Template reuse across cases
- Synthetic portrait generation
- Structural inconsistencies in documents
A Practical Step: Lookback Analysis
One of the most powerful ways organizations can understand their true exposure is through lookback analysis.
Instead of only screening new applications, institutions analyze their existing document archives to detect:
- Manipulated documents
- Synthetic IDs
- Reused images across claims or applications
- Fraud patterns across multiple customers
This provides a clear fraud exposure report and allows organizations to strengthen underwriting, claims, and compliance controls.
A Call to Action
The OnlyFake case is a reminder that document fraud is evolving rapidly — and that the scale of the problem is larger than most institutions realize.
If you are a bank, lender, or insurance company, a useful first step is to scan your existing document database.
Lookback analysis can reveal:
- The real percentage of manipulated documents in your portfolio
- Fraud patterns across customers
- Hidden risk already sitting inside approved applications or claims
Organizations that understand their exposure can respond faster, improve risk models, and prevent future losses.
The question is no longer if manipulated documents exist in your portfolio.
The real question is:
How many?